Studies in Intelligence: New Articles from The CIA’s In-House Journal
Unofficial Intelligence Community Views on Assassinations, James Angleton's 'Monster Plot,' Agent Protection, and More

The Presidential ban against CIA assassinations of foreign leaders, first enacted in 1976, reflected both moral and practical reasons — including concerns about retaliation against U.S. leaders — according to an article in the CIA’s in-house journal posted today by the National Security Archive. However, the U.S. government never spelled out the exact scope of the prohibition — at least by the time the article was written 20 years later — leaving U.S. presidents free to authorize the CIA to encourage foreign coups and engage in other operations “that endanger the lives of others,” according to the article.
First printed in the journal Studies in Intelligence in 1996, the piece was obtained through the Freedom of Information Act. It is one of 19 previously unreleased (including secret) journal items posted on the Web today for the first time, providing remarkable new details from insider perspectives, including:
- A proposal for a far more draconian version of the Intelligence Identities Protection Act – including secret courts for intelligence officers accused of violating that law and criminalizing any revelation or purported revelation of a covert intelligence officer’s identity. (Document 7)
- A description of how President Kennedy ordered Director of Central Intelligence John McCone to halt his effort to launch a second investigation of the actions of U-2 pilot Francis Gary Powers — who had been shot down during a May 1, 1960 overflight of the Soviet Union. (Document 11)
- An account of how CIA and Army intelligence analyses in the late 1970s indicated that the U.S. had significantly underestimated North Korean military strength — and derailed President Carter’s plan to withdraw U.S. ground forces from South Korea. (Document 2)
- A description of the evolution of the CIA’s role in counterterrorism — with the Directorate of Operations initially being the primary component dealing with terrorist issues, and the Directorate of Intelligence eventually emerging in a leading role. (Document 17)
- A 2004 interview with current Director of the Central Intelligence Agency, John Brennan. (Document 15)
Archive Senior Fellow Jeffrey T. Richelson, who obtained the materials and authored the accompanying essay, commented: “Written by intelligence professionals, these articles are a window through which to glean new information and perspectives on the U.S. Intelligence Community, past and present.”
The CIA began publishing Studies in Intelligence in 1955 to help build an understanding within the agency of the intelligence profession based on the insights and recollections of practitioners. The items in today’s posting fall into a number of categories — legal issues, intelligence analysis, CIA-NSA relations, counterintelligence, interviews, intelligence support and liaison, and odds & ends.
* * *
New Revelations from Studies in Intelligence Articles
By Dr. Jeffrey T. Richelson
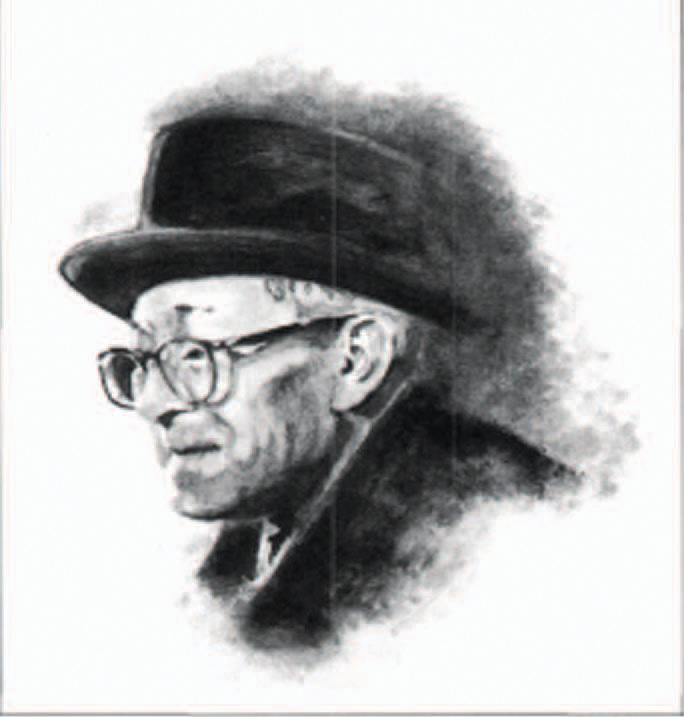
Sherman Kent, the “father of intelligence analysis,” with the inaugural issue of Studies in Intelligence. (Photo credit: CIA)
In 1955, at the suggestion of Sherman Kent, the head of the Board of National Estimates, the CIA launched a classified journal, titled Studies in Intelligence, “to promote a sense of professional identity, enhance proficiency, and build knowledge of intelligence cumulatively from the shared insights of its practitioners.”1The journal soon evolved into a quarterly containing articles whose classification, with rare exceptions, ranged from Unclassified to Secret. While the articles are not official statements of CIA or federal government views or policy, they do represent the thinking and recollections of an assortment of intelligence professionals.
Eventually, the CIA began declassifying some of the articles and releasing them to the National Archives and Records Administration (NARA). In 1992, the agency also published its first unclassified edition of Studies — available to anyone interested. In 2002, the CIA began posting on its website unclassified articles from classified issues of Studies — a practice that continues to this day.
Today, information about and copies of Studies articles can be found on the CIA website – in addition to the 1992 and beyond material. They appear in an index of declassified articles (which apparently only lists articles declassified by the CIA at its initiative); other indices which allow direct access to some of the declassified articles; and the CREST/Electronic Reading Room collection. Apparently not available electronically are articles that have been declassified in response to FOIA/Mandatory Declassification Requests or litigation.
Over the last decade, the author filed a series of FOIA requests, starting with a 2002 request for tables of contents of 1997-2002 issues of Studies as well as any unclassified articles that appeared in those issues. (As noted above, the CIA did not post unclassified articles from classified issues until sometime in 2002). Subsequent requests covered tables of contents for 1985-1996, and years subsequent to 2003. Tables of contents for those and other years were also obtained via litigation by the National Security Counselors organization.2
Classified articles of interest whose titles appeared in the declassified tables of contents were then requested under the FOIA. Today’s collection consists of articles obtained from those requests as well as some of the unclassified articles obtained from the 2002 request.
The collection would be more extensive had the CIA not denied, over a period of two years, requests (in their entirety) for 17 of 20 articles.3
The 19 posted articles in this briefing book can be grouped into a number of categories — legal issues, intelligence analysis, CIA-NSA relations, counterintelligence, interviews, intelligence support and liaison, and odds & ends.
LEGAL
 John Brennan, currently CIA director, previously served as director of the Terrorist Threat Integration Center. (Photo credit: CIA)
John Brennan, currently CIA director, previously served as director of the Terrorist Threat Integration Center. (Photo credit: CIA)
Legal issues covered in these Studies articles include prepublication review, the protection of the identities of U.S. intelligence officers, and assassination. The prepublication review process is treated (Document 18) by a former Directorate of Intelligence representative to the Publications Review Board, who offers an anodyne view of the process and an extensive list of “myths and realities.”4
The protection of intelligence officer identities is the subject of two articles. One (Document 8) provides a history of the Intelligence Identities Protection Act (IIPA) — from initial proposals, through opposition and revisions, to final passage. Another (Document 7) suggests that the legislation did not go nearly far enough. Thus, the author, who served as a law clerk in the CIA’s Office of General Counsel, asks: “if an intelligence officer may sign away his First Amendment right to free speech, then cannot the same officer also contract away his Sixth Amendment right to a public court?”
With respect to journalists, the author also suggests removing the limitations of the IIPA in prosecuting those who reveal the identity of a covert intelligence officer. While numerous newspapers and books have stated that the IIPA prohibits such disclosure, it actually only prohibits the disclosure by those who have had authorized access to such an identity (e.g. John Kiriakou) or who engage in a “pattern of activities” which seek to undermine/expose the U.S. intelligence effort.5 The author suggests criminalizing not only any disclosure but any purported disclosure – so that even an erroneous disclosure would be a criminal offense. Further, his suggested wording for amended legislation would seem to leave open the possibility of prosecution for disclosing information that might lead to such identification even if it was not explicit.
A 1996 article (Document 1) is a significant contrast to post-9/11 legal issues concerning targeted killings. Its focus is on the implications of the prohibition on assassination that appeared in President Gerald Ford’s 1976 executive order and subsequent executive orders on intelligence.6The article addresses the implications with regard to support for paramilitary operations, coup preparations (addressing the specific case of Panama and Gen. Manual Noriega), counterproliferation operations, and even deception operations directed at individuals — which might result in their imprisonment, torture, or execution by their own government. This is in sharp contrast to the discussion of legal issues in the Justice Department’s white paper on targeted killings, which focuses on the legal justification for a targeted killing of a U.S. citizen.
INTELLIGENCE ANALYSIS
Four articles deal with various aspects of intelligence analysis. In one case (Document 9), the article focuses on a subject of concern to many intelligence analysts during the Cold War – the cost of Soviet defense programs and the burden they imposed on the Soviet economy. Another (Document 13) examines intelligence analysis related to the Strategic Defense Initiative and successor missile defense programs.
A third article (Document 2), is the result of a CIA-funded study at the John F. Kennedy School of Government at Harvard — and illustrates the decades-long difficulty of producing reliable studies and estimates concerning North Korea. It examines the intelligence estimates produced by the CIA and Army concerning North Korean military strength — which significantly altered previous conclusions – and how they ultimately derailed President Carter’s plan to withdraw U.S. ground forces from South Korea.
Also, of contemporary relevance is the article (Document 17) on the inception and evolution of terrorism analysis in the CIA. The author notes that there was little pressure on the agency to produce terrorism analysis during its first quarter-century, and products such as the 1968 special national intelligence estimate, Terrorism and Internal Security in Israel and Jordan “were relative rarities.” The article goes on to describe increasing policy maker interest subsequent to the 1972 murder of Israeli Olympic athletes, and resulting Intelligence Community focus on the issue. He also describes how initially the Directorate of Operations’ clandestine collection activities were the principal element of the CIA’s counterterrorism activities — before the emergence of the Directorate of Intelligence as a key player in that effort.
CIA & NSA
James Jesus Angleton, head of counterintelligence and “CIA’s answer to the Delphic Oracle” from 1954-1974. (Photo credit: CIA)
Various works on intelligence have noted both the past competition and present cooperation between the CIA and National Security Agency.7 In “A Brave, New World” (Document 14), the author states that the CIA and NSA “are moving their strategic partnership beyond the optional cooperation of the past into a new era of collaboration,” and notes that the Director of Central Intelligence – George J. Tenet at the time – had viewed much of the success against al-Qaeda and its allies as the “direct result of CIA and NSA working together.”
He goes on to examine the origins of CIA-NSA discomfort in World War II and beyond, barriers to partnership, hints of change, the impact of the September 11, 2001 attacks, tangible results, asks if the partnership would last, and addresses the challenges ahead. Among the challenges identified are the development of joint strategic planning forums, increasing the pace and scope of efforts to find joint solutions to technical problems, and the incorporation of the concerns of line officers.
COUNTERINTELLIGENCE
Two articles address counterintelligence issues during very different portions of the CIA’s history. One (Document 19) addresses the roles of CIA counterintelligence chief (1954-1974) James J. Angleton and KGB defector Anatoliy Golitsyn in promulgating the thesis of widespread and successful Soviet deception against the West (the “Monster Plot”) and their impact on CIA operations and personnel. Among those whose lives or careers suffered were former KGB officer Alexandr Cherepanov (who was executed after the U.S. embassy returned materials he had provided), Yuri Nosenko (who was incarcerated by the CIA), and CIA officers Richard Kovich and David Murphy, who would each come under suspicion of being a Soviet mole. 8
Another treatment of counterintelligence (Document 16), by former chief of the National Clandestine Service Michael J. Sulick, focuses on counterintelligence in the counterterrorist effort. He argues that, because of how history played out, while counterintelligence failures during the Cold War were never exploited by the Soviet Union to launch attacks, similar failures against terrorist groups could result in “catastrophic” damage. Sulick goes on to discuss several topics: how terrorist groups operate like intelligence services; terrorist attempts to infiltrate their targets; the fact that there are now “more employees to worry about” because “personnel and facilities must also be defended from individuals with minimal or no clearance;” terrorist denial and deception; intelligence sharing; and further steps to be taken.
INTERVIEWS
Numerous issues of Studies have contained interviews with former or current senior intelligence personnel. In 1999, Studies published an extensive interview with John M. McMahon (Document 11), who joined the CIA in 1951, and eventually became Deputy Director for Operations, Deputy Director for Intelligence, and finally Deputy Director of Central Intelligence before retiring in 1986.
The interview covers his first years with the CIA in Germany, the U-2 program, the battle during the 1960s with the National Reconnaissance Office over satellite reconnaissance systems, a number of his senior positions (including DDO, DDI, and DDCI), relations with Congress, and covert action with regard to Iran and Afghanistan. With regard to U-2 pilot Francis Gary Powers (who was shot down in May 1960 over the Soviet Union, captured, and subsequently exchanged), he “did exactly what he was told,” McMahon noted. He went on to state that DCI John McCone was not convinced and planned to have Powers investigated for a second time – by the Air Force Office of Special Investigations – until President John F. Kennedy called McCone and ordered him not to pursue the matter.
The following year, Studies published an interview with then NSA director Lt. Gen. Michael V. Hayden (Document 12). Hayden spoke, inter alia, about his attempts to bring significant change to NSA, the impact of telecommunications change on NSA ( “our technological adversary is not a nation state but the global telecommunications industry”), the relationship between NSA and CIA, signals intelligence requirements, and limitations on NSA support to military commanders.
In 2004, current Director of the Central Intelligence Agency and then-director of the Terrorist Threat Integration Center (the predecessor of the National Counterterrorism Center) John Brennan was interviewed by Studies (Document 15) — an interview which focused on terrorism analysis. Brennan noted the TTIC had access to 26 unclassified and classified networks, and discussed whether “counterterrorism analysis” would represent a distinct career track; TTIC organization and practices as a model for the Intelligence Community; the need to break down the distinction between foreign and domestic intelligence; the distribution of terrorism analysis in the Intelligence Community; and information sharing.
INTELLIGENCE SUPPORT & LIAISON
Three articles deal with three aspects of intelligence support and liaison. One focuses on intelligence support to Congress, another on support to policymakers, and the third on support to military commanders. In “CIA’s Intelligence Sharing with Congress” (Document 3), the author describes “the phenomenon of the President’s own finished intelligence being used by Congress to question and attack the President’s foreign policy initiatives.” Specific examples include Indochina (during the Nixon administration), the Persian Gulf, and Haiti.
CIA support to executive branch policymakers is the subject of a 1998 article (Document 6), written by a CIA official who spent two years as the agency’s liaison to the State Department’s Ambassador-at-Large for the New Independent States — a position established “to improve the CIA’s ability to understand the policy priorities and concerns of the bureau.” Half of the four-page article is devoted to the author’s specification of six ways in which CIA support for senior policymakers could be improved — which include “living with the customer” and “early bird service.”
Intelligence support to military forces, in the form of National Intelligence Support Teams (NISTs) is the subject of an article (Document 5) in a 1998 issue of Studies. The author reviews the background and operation of NISTs, which combined personnel and provided support from key national and defense intelligence agencies (including CIA, the Defense Intelligence Agency, the National Security Agency, and the National Imagery and Mapping Agency) and provide support to commanders of joint task forces such as those involved with Operations UPHOLD DEMOCRACY (Haiti) and JOINT ENDEAVOR (Bosnia). In addition, the author makes a number of suggestions for improvements.
ODDS & ENDS
 Ribbon-cutting ceremony at the Terrorist Threat Integration Center, May 1, 2003. (Photo credit: FBI)
Ribbon-cutting ceremony at the Terrorist Threat Integration Center, May 1, 2003. (Photo credit: FBI)Two additional articles concern events separated by over two hundred years. One (Document 4), focuses on Britain’s penetration of the United States diplomatic mission to France during the Revolutionary War. Penetration involved British recruiting of agents with access to mission members, theft of a mission member’s journal and Britain’s control of agents ostensibly operating on behalf of the United States.
In November 1990, at its Langley headquarters, the CIA dedicated an encrypted sculpture named ‘Kryptos’ – a structure with several messages carved into its surface, but messages whose content was concealed through encryption. [Since that time three of the four messages contained in the sculpture have been solved.9 One of the individuals, from the Directorate of Intelligence, in a 1999 article (Document 10) a member of the Directorate of Intelligence describes his work in decrypting the message.
THE DOCUMENTS
Document 1: [Deleted], “Covert Action, Loss of Life and the Prohibition on Assassination, 1976-1996,” Studies in Intelligence, 40, 2 (1996). Classification Not Available.
Source: CIA Freedom of Information Act Release.
In this article, the author examines the effect of the decision no longer to employ assassination as an instrument of U.S. policy, and the issues the prohibition raised with respect to other CIA activities that might result in the loss of life. These include lethal operations that directly risk the loss of life, lethal operations indirectly risking loss of life (e.g. demolition of a facility when it is believed to be unoccupied), and nonlethal operations (e.g. deception) directed at identifiable persons.
Document 2: Joe Wood, “Persuading a President: Jimmy Carter and American Troops in Korea,” Studies in Intelligence, 40, 4 (1996). Classification Not Available.
Source: CIA Freedom of Information Act Release.
During his 1976 presidential campaign, Jimmy Carter promised to withdraw U.S. ground forces from South Korea. This article is the result of a case study prepared at Harvard’s John F. Kennedy School of Government, and funded by the CIA. It reports on the intelligence estimates and studies on North Korean military strength produced early in Carter’s administration, and how those estimates resulted in U.S. forces remaining in South Korea.
Document 3: [Deleted], “CIA’s Intelligence Sharing With Congress,” Studies in Intelligence, 41, 3 (1997). Classification Not Available.
Source: CIA Freedom of Information Act Release.
This short article focuses on “the phenomenon of the President’s own intelligence being used to question and attack the President’s foreign policy initiatives.” Specific cases discussed concern Indochina, the Persian Gulf, and Haiti.
Document 4: [Deleted], “British Penetration of America’s First Diplomatic Mission,”Studies in Intelligence, 41, 4 (1997). Classification Not Available.
Source: CIA Freedom of Information Act Release.
The focus of this article is Britain’s penetration of the U.S. diplomatic mission in Paris during the Revolutionary War. Successes included recruiting several access agents to provide intelligence on mission activities as well as the theft of the journal of mission member Arthur Lee, and the mission’s “recruiting” agents who were actually under British control.
Document 5: Capt. James M. Lose, “The National Intelligence Support Team,” Studies in Intelligence, 42, 1 (1998) . Unclassified.
Source: CIA Freedom of Information Act Release.
The author reviews the background and operation of National Intelligence Support Teams (NISTs) — combining personnel from key national and defense intelligence agencies (including CIA, the Defense Intelligence Agency, the National Security Agency, and the National Imagery and Mapping Agency) — which provided support to commanders of joint task forces such as those involved with Operations UPHOLD DEMOCRACY (Haiti) and JOINT ENDEAVOR (Bosnia). In addition, the author makes a number of suggestions for improvements.
Document 6: [Deleted], “Increasing CIA’s Value Added to the Senior Policymaker,” Studies in Intelligence, 42, 2 (1998). Unclassified
Source: CIA Freedom of Information Act Release.
This article is based on the author’s two years serving as the CIA’s liaison to a State Department component and focuses on his suggestions for increasing the CIA’s value to policymakers — including “living with the customer,” better service for “second tier” officials, one-stop shopping for “the facts,” stronger community partnerships, and “early bird” service.
Document 7: [Deleted], “Legislative and Judicial Safeguards for US Intelligence Personnel,” Studies in Intelligence, 42, 2 (1998). Unclassified.
Source: CIA Freedom of Information Act Release.
The author, who served as a law clerk with the CIA’s Office of the General Counsel, examines the history and enforcement of the Intelligence Identities Protection Act (IIPA), as well as exploring a number of options to enhance the protection of US intelligence personnel — including secret trials, and amending the IIPA to allow criminal penalties for any individual who reveals or purports to reveal the identity of covert intelligence personnel.
Document 8: [Deleted], “Passing the Intelligence Identities Protection Act of 1982,”Studies in Intelligence, 42, 3 (1998). Unclassified
Source: CIA Freedom of Information Act Release.
This article provides a short history of the background behind the IIPA, the initial proposals for a law criminalizing the revelation of the identify of covert intelligence personnel, the various attempts to pass such legislation, opposition to some proposed provisions, and the ultimate passage of the IIPA.
Document 9: [Deleted], “Analyzing Soviet Defense Program, 1951-1990,” Studies in Intelligence, 42, 3 (1998). Unclassified
Source: CIA Freedom of Information Act Release.
This article focuses on what was a major concern of some intelligence analysts during the Cold War — determining the actual cost of Soviet defense programs and the burden they placed on the Soviet economy. Among the author’s assertions was that “in every case, the [Intelligence Community] concluded that Soviet economic difficulties would impinge only marginally, if at all, on Soviet defense plans” and that “Only when Gorbachev’s perestroika was foundering was the idea of economic constraints on the defense budget gain a foothold in the national estimates arena, and even then the majority opinion rejected the notion that the USSR would unilaterally reduce its defense spending as it did in 1989.”
Document 10: [Deleted], “Cracking the Courtyard Crypto,” Studies in Intelligence, 43, 1 (1999). Unclassified.
Source: CIA Freedom of Information Act Release.
In 1990, the CIA unveiled a sculpture name “Kryptos” in the agency’s courtyard — a sculpture whose surface was covered with an encrypted message. This article, by a member of the Directorate of Intelligence, describes the process by which he deciphered most of the message.
Document 11: [Deleted], “An Interview with Former DDCI John N. McMahon,” Studies in Intelligence, 43, 1 (1999). Classification Not Available.
Source: CIA Freedom of Information Act Release.
This interview, with John N. McMahon, who joined the CIA in 1951 and served in a variety of positions before he retired in 1986, covers his early days in the agency, the U-2 program, battles over satellite reconnaissance systems, as well as his tours as head of the clandestine service, the intelligence directorate, and as Deputy Director for Central Intelligence. In addition, he discusses the CIA-Congressional relationship as well as covert action with regard to Iran and Afghanistan.
Document 12: [Deleted], “An Interview with NSA Director Lt. Gen. Michael V. Hayden,”Studies in Intelligence , 44, 1 (2000). Secret/[Deleted]
Source: CIA Freedom of Information Act Release.
In this interview, Michael Hayden, then the director of the National Security Agency, discusses his attempt to bring significant change to NSA, his belief that “our technological adversary is not a nation state but the global telecommunications industry,” the relationship between NSA and the CIA (also discussed in Document 14), and other topics.
Document 13: [Deleted], “Intelligence and US Missile Defense Planning,” Studies in Intelligence, 45, 2 (2001). Classification Not Available .
Source: CIA Freedom of Information Act Release.
After providing a brief introduction to the early origins of missile defense, this article addresses the establishment of the Strategic Defense Initiative, the post-Cold War shift in U.S. missile defense emphasis and the challenges of providing intelligence on threats, technical issues, and foreign reactions.
Document 14: [Deleted], “A Brave, New World,” Studies in Intelligence, 48, 2 (2004).Classification Not Available .
Source: CIA Freedom of Information Act Release.
This article addresses the relationship between the CIA and National Security Agency in the aftermath of the September 11, 2001 terrorist attacks. It notes the origins of CIA-NSA enmity going back to World War II, barriers that have existed to a partnership between the two agencies, hints of change in the late 1990s, and the impact of 9/11. Its final sections focus on tangible results, the likelihood that the partnership will last, and the challenges ahead.
Document 15: [Deleted], “An Interview with TTIC Director John Brennan,” Studies in Intelligence, 48. 4 (2004). Secret.
Source: CIA Freedom of Information Act Release.
This interview with John Brennan, currently the Director of the Central Intelligence Agency, was conducted in 2003 — when he was the director of the Terrorist Threat Integration Center (which was subsequently absorbed by the National Counterterrorism Center). Questions include those about the center’s access to intelligence data, counterterrorism analysis as a specialty, the different components of the Intelligence Community involved in counterterrorism analysis, and the division of responsibilities for different aspects of counterterrorism analysis.
Document 16: Michael J. Sulick, “Counterintelligence in the War Against Terrorism,”Studies in Intelligence, 48, 4 (2004). Secret/[Deleted].
Source: CIA Freedom of Information Act Release.
The author, who served as CIA Associate Deputy Director for Operations and became chief of the National Clandestine Service in 2007, notes that whereas U.S. counterintelligence defeats during the Cold War were never exploited by the Soviet Union in an actual war, terrorists “can immediately exploit information gained through espionage to launch attacks.” He goes on to explore the subjects of “terrorists as intelligence operatives;” “exposing terrorist spies;” “more employees to worry about;” terrorist denial and deception; intelligence sharing; and further actions.
Document 17: [Deleted], “Terrorism Analysis in the CIA: The Gradual Awakening (1972-80),” Studies in Intelligence, 51, 1 (2007). Secret.
Source: CIA Freedom of Information Act Release.
This article, after discussing the emergence of terrorism as an international issue, traces the development of terrorism analysis in the CIA from the Truman to Nixon administrations. It covers increased policymaker interest in the subject (particularly following the murder of Israeli Olympic athletes by Palestinian terrorists in 1972), and the resulting increased Intelligence Community interest; the initially ascendant role of the Directorate of Operations; the Directorate of Intelligence’s subsequent larger role in terrorism analysis; and early analytical challenges.
Document 18: [Deleted], “CIA Prepublication Review in the Information Age,” Studies in Intelligence, 55, 3 (September 2011). Confidential.
Source: CIA Freedom of Information Act Release.
The author, who served as the first senior representative of the Directorate of Intelligence on the CIA Publication Review Board (PRB) offers an anodyne view of the publication review process. Topics covered include the origins and evolution of the PRB and review process, the impact of a vast increase in the number of submitted manuscripts, the meaning of the ‘appropriateness’ requirement, and “myths and realities of the process.” Asserted myths included that “the prepublication review process is unfair, arbitrary, capricious” and that “the PRB often doesn’t know what has already been released.”
Document 19: [Deleted], “James J. Angleton, Anatoliy Golitsyn, and the ‘Monster Plot’: Their Impact on CIA Personnel and Operations,” Studies in Intelligence, 55, 4 (December 2011). Secret.
Source: CIA Freedom of Information Act Release.
This article examines the roles of CIA counterintelligence chief James J. Angleton and KGB defector Anatoliy Golitsyn in the formulation of the “Monster Plot” — which asserted that the Soviet Union had conducted decades-long, massive and successful deception operations against the West, including the use of false defectors and volunteers. It then examines the impact of Angleton and Golitsyn’s thinking on a number of cases and individuals — including Yuriy Nosenko, Lee Harvey Oswald, and several CIA officers who were alleged to be possible Soviet moles.
NOTES
1. H, Bradford Westerfield, Inside CIA’s Private World: Declassified Articles from the Agency’s Internal Journal, 1955-1992 (New Haven: Yale University Press, 1995), pp. vii, xii-xiv.
2. The tables of contents, starting with the initial issue of Studies, can be found atwww.nationalsecuritylaw.org. A significant disparity existed between the CIA’s response to the 2010 FOIA request for 1985-1996 tables of contents and their response to National Security Counselors litigation. Approximately 130 more titles were released in response to litigation than to the author’s FOIA request. Some of the titles not released in response to the FOIA request but produced under litigation include: “Psychology of Treason,” “The Decline and Fall of the Shah,” “On Analytic Success and Failure,” “The DI’s Organizational Culture,” and “Observation Balloons and Reconnaissance Satellites.” “Psychology of Treason” actually appeared in the Westerfield collection (pp. 70-82) while “Observation Balloons and Reconnaissance Satellite” had been released in its entirety and could be found on the CIA’s website.
3. Articles denied in their entirety included “Overhead Imagery during the Yom Kippur War,””The Origins and Applications of Nuclear Intelligence,” “Sifting the Evidence on Vitaly Yurchenko,” “Iraq’s Nuclear Weapons Program,” and “The Need for Improved Strategic Counterintelligence Analysis.”
4. Various authors have found the PRB process less than reasonable. For example, see David H.Sharp, The CIA’s Greatest Covert Operation: Inside the Daring Mission to Recover a Nuclear-Armed Soviet Sub (Lawrence, Ks.: University Press of Kansas, 2012), pp. xi-xii; Robert Wallace and H. Keith Melton, Spycraft: The Secret History of the CIA’s Spytechs from Communism to Al-Qaeda (New York: Dutton, 2008), pp. xx-xxi.
5. Thus, the new head of the National Clandestine Service, who is still officially undercover, as well as the temporary head (also undercover) have been named without a violation of the law. See “CIA’s New Chief Spy Outed on Twitter,” www.gawker.com, accessed May 9, 2013.
6. Although it is often assumed that the first prohibition of assassination was Gerald Ford’s 1976 executive order, DCI’s Richard Helms and successor William Colby had issued internal directives prohibiting such action – Richard Helms, “Allegations of Assassinations,” March 6, 1972; William E. Colby, Subject: Policy Against Assassination,, August 29, 1973.
7. For example, see James R. Taylor, Deputy Director of Operations, National Security Agency, Subject: Thoughts on Strategic Issues for the Institution, April 9, 1999, Document 21 in Jeffrey T. Richelson (ed.), NSA Electronic Briefing Book #24, The NSA Declassified , March 11,2005,www.gwu.edu/~nsarchive/NSAEBB/NSAEBB24.
8. Two major accounts of Angleton and the Molehunt are: Tom Mangold, Cold Warrior – James Jesus Angleton: The CIA’s Master Spy Hunter (New York: Simon & Schuster, 1991), and David Wise, Molehunt: The Secret Search for Traitors that Shattered the CIA (New York: Random House, 1992).
9. On Kryptos, see “Flash Movie Text,” www.ciagov, accessed May 6, 2013; “Kryptos,” http://en.wikipedia.org/wiki/Kryptos.