Image Professor Peter Dale Scott
This article was originally published in November 2011
“I know the capacity that is there to make tyranny total in America, and we must see to it that this agency [the National Security Agency] and all agencies that possess this technology operate within the law and under proper supervision, so that we never cross over that abyss. That is the abyss from which there is no return.” — Senator Frank Church (1975)
I would like to discuss four major and badly understood events – the John F. Kennedy assassination, Watergate, Iran-Contra, and 9/11. I will analyze these deep events as part of a deeper political process linking them, a process that has helped build up repressive power in America at the expense of democracy.
In recent years I have been talking about a dark force behind these events — a force which, for want of a better term, I have clumsily called a “deep state,” operating both within and outside the public state. Today for the first time I want to identify part of that dark force, a part which has operated for five decades or more at the edge of the public state. This part of the dark force has a name not invented by me: the Doomsday Project, the Pentagon’s name for the emergency planning “to keep the White House and Pentagon running during and after a nuclear war or some other major crisis.”1
My point is a simple and important one: to show that the Doomsday Project of the 1980s, and the earlier emergency planning that developed into it, have played a role in the background of all the deep events I shall discuss.
More significantly, it has been a factor behind all three of the disturbing events that now threaten American democracy. The first of these three is what has been called the conversion of our economy into a plutonomy – with the increasing separation of America into two classes, into the haves and the have-nots, the one percent and the 99 percent. The second is America’s increasing militarization, and above all its inclination, which has become more and more routine and predictable, to wage or provoke wars in remote regions of the globe. It is clear that the operations of this American war machine have served the one percent.2
The third – my subject today — is the important and increasingly deleterious impact on American history of structural deep events: mysterious events, like the JFK assassination, the Watergate break-in, or 9/11, which violate the American social structure, have a major impact on American society, repeatedly involve law-breaking or violence, and in many cases proceed from an unknown dark force.
There are any number of analyses of America’s current breakdown in terms of income and wealth disparity, also in terms of America’s increasing militarization and belligerency. What I shall do today is I think new: to argue that both the income disparity – or what has been called our plutonomy — and the belligerency have been fostered significantly by deep events.
We must understand that the income disparity of America’s current economy was not the result of market forces working independently of political intervention. In large part it was generated by a systematic and deliberate ongoing political process dating from the anxieties of the very wealthy in the 1960s and 1970s that control of the country was slipping away from them.
This was the time when future Supreme Court Justice Lewis Powell, in a 1971 memorandum, warned that survival of the free enterprise system depended on “careful long-range planning and implementation” of a well-financed response to threats from the left.3 This warning was answered by a sustained right-wing offensive, coordinated by think tanks and funded lavishly by a small group of family foundations.4 We should recall that all this was in response to serious riots in Newark, Detroit, and elsewhere, and that increasing calls for a revolution were coming from the left (in Europe as well as America). I will focus today on the right’s response to that challenge, and on the role of deep events in enhancing their response.
What was important about the Powell memorandum was less the document itself than the fact that it was commissioned by the United States Chamber of Commerce, one of the most influential and least discussed lobbying groups in America. And the memorandum was only one of many signs of that developing class war in the 1970s, a larger process working both inside and outside government (including what Irving Kristol called an “intellectual counterrevolution”), which led directly to the so-called “Reagan Revolution.”5
It is clear that this larger process has been carried on for almost five decades, pumping billions of right-wing dollars into the American political process. What I wish to show today is that deep events have also been integral to this right-wing effort, from the John F. Kennedy assassination in 1963 to 9/11. 9/11 resulted in the implementation of “Continuity of Government” (COG) plans (which in the Oliver North Iran Contra Hearings of 1987 were called plans for “the suspension of the U.S. constitution”). These COG plans, building on earlier COG planning, had been carefully developed since 1982 in the so-called Doomsday Project, by a secret group appointed by Reagan. The group was composed of both public and private figures, including Donald Rumsfeld and Dick Cheney.
I shall try to show today that in this respect 9/11 was only the culmination of a sequence of deep events reaching back to the Kennedy assassination if not earlier, and that the germs of the Doomsday Project can be detected behind all of them.
More specifically, I shall try to demonstrate about these deep events that
1) prior bureaucratic misbehavior by the CIA and similar agencies helped to make both the Kennedy assassination and 9/11 happen;
2) the consequences of each deep event included an increase in top-down repressive power for these same agencies, at the expense of persuasive democratic power;6
3) there are symptomatic overlaps in personnel between the perpetrators of each of these deep events and the next;
4) one sees in each event the involvement of elements of the international drug traffic – suggesting that our current plutonomy is also to some degree a narconomy;
5) in the background of each event (and playing an increasingly important role) one sees the Doomsday Project — the alternative emergency planning structure with its own communications network, operating as a shadow network outside of regular government channels.
Bureaucratic Misbehavior as a Factor Contributing to both the JFK Assassination and 9/11
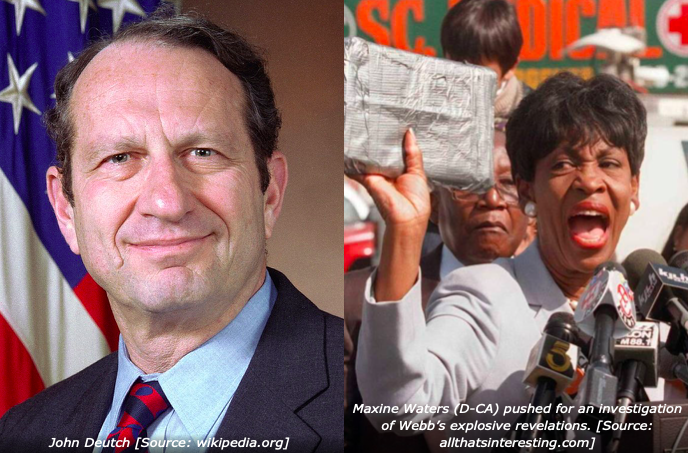
Both the JFK assassination and 9/11 were facilitated by the way the CIA and FBI manipulated their files about alleged perpetrators of each event (Lee Harvey Oswald in the case of what I shall call JFK, and the alleged hijackers Khalid al-Mihdhar and Nawaf al-Hazmi in the case of 9/11). Part of this facilitation was the decision on October 9, 1963 of an FBI agent, Marvin Gheesling, to remove Oswald from the FBI watch list for surveillance. This was shortly after Oswald’s arrest in New Orleans in August and his reported travel to Mexico in September. Obviously these developments should normally have made Oswald a candidate for increased surveillance.7
This misbehavior is paradigmatic of the behavior of other agencies, especially the CIA, in both JFK and 9/11. Indeed Gheesling’s behavior fits very neatly with the CIA’s culpable withholding from the FBI, in the same month of October, information that Oswald had allegedly met in Mexico City with a suspected KGB agent, Valeriy Kostikov.8 This also helped ensure that Oswald would not be placed under surveillance. Indeed, former FBI Director Clarence Kelley in his memoir later complained that the CIA’s withholding of information was the major reason why Oswald was not put under surveillance on November 22, 1963.9
A more ominous provocation in 1963 was that of Army Intelligence, one unit of which in Dallas did not simply withhold information about Lee Harvey Oswald, but manufactured false intelligence that seemed designed to provoke retaliation against Cuba. I call such provocations phase-one stories, efforts to portray Oswald as a Communist conspirator (as opposed to the later phase-two stories, also false, portraying him as a disgruntled loner). A conspicuous example of such phase-one stories is a cable from the Fourth Army Command in Texas, reporting a tip from a Dallas policeman who was also in an Army Intelligence Reserve unit:
Assistant Chief Don Stringfellow, Intelligence Section, Dallas Police Department, notified 112th INTC [Intelligence] Group, this Headquarters, that information obtained from Oswald revealed he had defected to Cuba in 1959 and is a card-carrying member of Communist Party.”10
This cable was sent on November 22 directly to the U.S. Strike Command at Fort MacDill in Florida, the base poised for a possible retaliatory attack against Cuba.11
The cable was not an isolated aberration. It was supported by other false phase-one stories from Dallas about Oswald’s alleged rifle, and specifically by concatenated false translations of Marina Oswald’s testimony, to suggest that Oswald’s rifle in Dallas was one he had owned in Russia.12
These last false reports, apparently unrelated, can also be traced to officer Don Stringfellow’s 488th Army Intelligence Reserve unit.13 The interpreter who first supplied the false translation of Marina’s words, Ilya Mamantov, was selected by a Dallas oilman, Jack Crichton, and Deputy Dallas Police Chief George Lumpkin.14 Crichton and Lumpkin were also the Chief and the Deputy Chief of the 488th Army Intelligence Reserve unit.15 Crichton was also an extreme right-winger in the community of Dallas oilmen: he was a trustee of the H.L. Hunt Foundation, and a member of the American Friends of the Katanga Freedom Fighters, a group organized to oppose Kennedy’s policies in the Congo.
We have to keep in mind that some of the Joint Chiefs were furious that the 1962 Missile Crisis had not led to an invasion of Cuba, and that, under new JCS Chairman Maxwell Taylor, the Joint Chiefs, in May 1963, still believed “that US military intervention in Cuba is necessary.”16 This was six months after Kennedy, to resolve the Missile Crisis in October 1962, had given explicit (albeit highly qualified) assurances to Khrushchev, that the United States would not invade Cuba.17 This did not stop the J-5 of the Joint Chiefs of Staff (the JCS Directorate of Plans and Policy) from producing a menu of “fabricated provocations to justify military intervention.”18 (One proposed example of “fabricated provocations” envisioned “using MIG type aircraft flown by US pilots to … attack surface shipping or to attack US military.”)19
The deceptions about Oswald coming from Dallas were immediately post-assassination; thus they do not by themselves establish that the assassination itself was a provocation-deception plot. They do however reveal enough about the anti-Castro mindset of the 488th Army Intelligence Reserve unit in Dallas to confirm that it was remarkably similar to that of the J-5 the preceding May – the mindset that produced a menu of “fabricated provocations” to attack Cuba. (According to Crichton there were “about a hundred men in [the 488th Reserve unit] and about forty or fifty of them were from the Dallas Police Department.”)20
It can hardly be accidental that we see this bureaucratic misbehavior from the FBI, CIA, and military, the three agencies with which Kennedy had had serious disagreements in his truncated presidency.21 Later in this paper I shall link Dallas oilman Jack Crichton to the 1963 emergency planning that became the Doomsday Project.
Analogous Bureaucratic Misbehavior in the Case of 9/11
Before 9/11 the CIA, in 2000-2001, again flagrantly withheld crucial evidence from the FBI: evidence that, if shared, would have led the FBI to surveil two of the alleged hijackers, Khalid al-Mihdhar and Nawaz al-Hazmi. This sustained withholding of evidence provoked an FBI agent to predict accurately in August, 2001, that “someday someone will die.”22 After 9/11 another FBI agent said of the CIA: “They [CIA] didn’t want the bureau meddling in their business—that’s why they didn’t tell the FBI…. And that’s why September 11 happened. That is why it happened. . . . They have blood on their hands. They have three thousand deaths on their hands”23 The CIA’s withholding of relevant evidence before 9/11 (which it was required by its own rules to supply) was matched in this case by the NSA.24
Without these withholdings, in other words, neither the Kennedy assassination nor 9/11 could have developed in the manner in which they did. As I wrote in American War Machine, it would appear that
Oswald (and later al-Mihdhar) had at some prior point been selected as designated subjects for an operation. This would not initially have been for the commission of a crime against the American polity: on the contrary, steps were probably taken to prepare Oswald in connection with an operation against Cuba and al-Mihdhar [I suspect] for an operation against al-Qaeda. But as [exploitable] legends began to accumulate about both figures, it became possible for some witting people to subvert the sanctioned operation into a plan for murder that would later be covered up. At this point Oswald (and by analogy al-Mihdhar) was no longer just a designated subject but also now a designated culprit.25
Kevin Fenton, in his exhaustive book Disconnecting the Dots, has since reached the same conclusion with respect to 9/11: “that, by the summer of 2001, the purpose of withholding the information had become to allow the attacks to go forward.”26 He has also identified the person chiefly responsible for the misbehavior: CIA officer Richard Blee, Chief of the CIA’s Bin Laden Unit. Blee, while Clinton was still president, had been one of a faction inside CIA pressing for a more belligerent CIA involvement in Afghanistan, in conjunction with the Afghan Northern Alliance.27 This then happened immediately after 9/11, and Blee himself was promoted, to become the new Chief of Station in Kabul.28
How CIA and NSA Withholding of Evidence in the Second Tonkin Gulf Incident, Contributed to War with North Vietnam
I will spare you the details of this withholding, which can be found in my American War Machine, pp. 200-02. But Tonkin Gulf is similar to the Kennedy assassination and 9/11, in that manipulation of evidence helped lead America – in this case very swiftly – into war.
Historians such as Fredrik Logevall have agreed with the assessment of former undersecretary of state George Ball that the US destroyer mission in the Tonkin Gulf, which resulted in the Tonkin Gulf incidents, “was primarily for provocation.”29 The planning for this provocative mission came from the J-5 of the Joint Chiefs of Staff, the same unit that in 1963 had reported concerning Cuba that, “the engineering of a series of provocations to justify military intervention is feasible.”30
The NSA and CIA suppression of the truth on August 4 was in the context of an existing high-level (but controversial) determination to attack North Vietnam. In this respect the Tonkin Gulf incident is remarkably similar to the suppression of the truth by CIA and NSA leading up to 9/11, when there was again a high-level (but controversial) determination to go to war.
Increases in Repressive Power After Deep Events
All of the deep events discussed above have contributed to the cumulative increase of Washington’s repressive powers. It is clear for example that the Warren Commission used the JFK assassination to increase CIA surveillance of Americans. As I wrote in Deep Politics, this was the result of
the Warren Commission’s controversial recommendations that the Secret Service’s domestic surveillance responsibilities be increased (WR 25-26). Somewhat illogically, the Warren Report concluded both that Oswald acted alone (WR 22), . . . and also that the Secret Service, FBI, CIA, should coordinate more closely the surveillance of organized groups (WR 463). In particular, it recommended that the Secret Service acquire a computerized data bank compatible with that already developed by the CIA.31
This pattern would repeat itself four years later with the assassination of Robert Kennedy. In the twenty-four hours between Bobby’s shooting and his death, Congress hurriedly passed a statute— drafted well in advance (like the Tonkin Gulf Resolution of 1964 and the Patriot Act of 2001) — that still further augmented the secret powers given to the Secret Service in the name of protecting presidential candidates.32
This was not a trivial or benign change: from this swiftly considered act, passed under Johnson, flowed some of the worst excesses of the Nixon presidency.33
The change also contributed to the chaos and violence at the Chicago Democratic Convention of 1968. Army intelligence surveillance agents, seconded to the Secret Service, were present both inside and outside the convention hall. Some of them equipped the so-called “Legion of Justice thugs whom the Chicago Red Squad turned loose on local anti-war groups.”34
In this way the extra secret powers conferred after the RFK assassination contributed to the disastrous turmoil in Chicago that effectively destroyed the old Democratic Party representing the labor unions: The three Democratic presidents elected since then have all been significantly more conservative.
Turning to Watergate and Iran-Contra, both of these events were on one level setbacks to the repressive powers exercised by Richard Nixon and the Reagan White House, not expansions of them. On the surface level this is true: both events resulted in legislative reforms that would appear to contradict my thesis of expanding repression.
We need to distinguish here, however, between the two years of the Watergate crisis, and the initial Watergate break-in. The Watergate crisis saw a president forced into resignation by a number of forces, involving both liberals and conservatives. But the key figures in the initial Watergate break-in itself – Hunt, McCord, G. Gordon Liddy, and their Cuban allies — were all far to the right of Nixon and Kissinger. And the end result of their machinations was not finalized until the so-called Halloween Massacre in 1975, when Kissinger was ousted as National Security Adviser and Vice-President Nelson Rockefeller was notified he would be dropped from the 1976 Republican ticket. This major shake-up was engineered by two other right-wingers: Donald Rumsfeld and Dick Cheney in the Gerald Ford White House.35
That day in 1975 saw the permanent defeat of the so-called Rockefeller or liberal faction within the Republican Party. It was replaced by the conservative Goldwater-Casey faction that would soon capture the nomination and the presidency for Ronald Reagan.36 This little-noticed palace coup, along with other related intrigues in the mid-1970s, helped achieve the conversion of America from a welfare capitalist economy, with gradual reductions in income and wealth disparity, into a financialized plutonomy where these trends were reversed.37
Again in Iran-Contra we see a deeper accumulation of repressive power under the surface of liberal reforms. At the time not only the press but even academics like myself celebrated the termination of aid to the Nicaraguan Contras, and the victory there of the Contadora peace process. Not generally noticed at the time was the fact that, while Oliver North was removed from his role in the Doomsday Project, that project’s plans for surveillance, detention, and the militarization of the United States continued to grow after his departure.38
Also not noticed was the fact that the US Congress, while curtailing aid to one small drug-financed CIA proxy army, was simultaneously increasing US support to a much larger coalition of drug-financed proxy armies in Afghanistan.39 While Iran-Contra exposed the $32 million which Saudi Arabia, at the urging of CIA Director William Casey, had supplied to the Contras, not a word was whispered about the $500 million or more that the Saudis, again at the urging of Casey, had supplied in the same period to the Afghan mujahedin.40 In this sense the drama of Iran-Contra in Congress can be thought of as a misdirection play, directing public attention away from America’s much more intensive engagement in Afghanistan – a covert policy that has since evolved into America’s longest war.
We should expand our consciousness of Iran-Contra to think of it as Iran-Afghan-Contra. And if we do, we must acknowledge that in this complex and misunderstood deep event the CIA in Afghanistan exercised again the paramilitary capacity that Stansfield Turner had tried to terminate when he was CIA Director under Jimmy Carter. This was a victory in short for the faction of men like Richard Blee, the protector of al-Mihdhar as well as the advocate in 2000 for enhanced CIA paramilitary activity in Afghanistan.41
Personnel Overlaps Between the Successive Deep Events
I will never forget the New York Times front-page story on June 18, 1972, the day after the Watergate break-in. There were photographs of the Watergate burglars, including one of Frank Sturgis alias Fiorini, whom I had already written about two years earlier in my unpublished book manuscript, “The Dallas Conspiracy” about the JFK assassination.
Sturgis was no nonentity: a former contract employee of the CIA, he was also well connected to the mob-linked former casino owners in Havana.42 My early writings on the Kennedy case focused on the connections between Frank Sturgis and an anti-Castro Cuban training camp near New Orleans in which Oswald had shown an interest; also in Sturgis’ involvement in false “phase-one” stories portraying Oswald as part of a Communist Cuban conspiracy.43
In spreading these “phase-one” stories in 1963, Sturgis was joined by a number of Cubans who were part of the CIA-supported army in Central America of Manuel Artime. Artime’s base in Costa Rica was closed down in 1965, allegedly because of its involvement in drug trafficking.44 In the 1980s some of these Cuban exiles later became involved in drug-financed support activities for the Contras.45
The political mentor of Artime’s MRR movement was future Watergate plotter Howard Hunt; and Artime in 1972 would pay for the bail of the Cuban Watergate burglars. The drug money-launderer Ramón Milián Rodríguez has claimed to have delivered $200,000 in cash from Artime to pay off some of the Cuban Watergate burglars; later, in support of the Contras, he managed two Costa Rican seafood companies, Frigorificos and Ocean Hunter, that laundered drug money.46
It is alleged that Hunt and McCord had both been involved with Artime’s invasion plans in 1963.47 It was I believe no accident that the organization of Hunt’s protégé Artime became enmired in drug trafficking. Hunt, I have argued elsewhere, had been handling a U.S. drug connection since his 1950 post in Mexico City as OPC (Office of Policy Coordination) chief.48
But McCord not only had a past in the anti-Castro activities of 1963, he was also part of the nation’s emergency planning network that would later figure so prominently in the background of Iran-Contra and 9/11. McCord was a member of a small Air Force Reserve unit in Washington attached to the Office of Emergency Preparedness (OEP); assigned “to draw up lists of radicals and to develop contingency plans for censorship of the news media and U.S. mail in time of war.”49 His unit was part of the Wartime Information Security Program (WISP), which had responsibility for activating “contingency plans for imposing censorship on the press, the mails and all telecommunications (including government communications) [and] preventive detention of civilian ‘security risks,’ who would be placed in military ‘camps.’”50 In other words, these were the plans that became known in the 1980s as the Doomsday Project, the Continuity of Government planning on which Dick Cheney and Donald Rumsfeld worked together for twenty years before 9/11.
A Common Denominator for Structural Deep Events: Project Doomsday and COG
McCord’s participation in an emergency planning system dealing with telecommunications suggests a common denominator in the backgrounds of almost all the deep events we are considering. Oliver North, the Reagan-Bush OEP point man on Iran-Contra planning, was also involved in such planning; and he had access to the nation’s top secret Doomsday communications network. North’s network, known as Flashboard, “excluded other bureaucrats with opposing viewpoints…[and] had its own special worldwide antiterrorist computer network, … by which members could communicate exclusively with each other and their collaborators abroad.”51
Flashboard was used by North and his superiors for extremely sensitive operations which had to be concealed from other dubious or hostile parts of the Washington bureaucracy. These operations included the illegal shipments of arms to Iran, but also other activities, some still not known, perhaps even against Olof Palme’s Sweden.52 Flashboard, America’s emergency network in the 1980s, was the name in 1984-86 of the full-fledged Continuity of Government (COG) emergency network which was secretly planned for twenty years, at a cost of billions, by a team including Cheney and Rumsfeld. On 9/11 the same network was activated anew by the two men who had planned it for so many years.53
But this Doomsday planning can be traced back to 1963, when Jack Crichton, head of the 488th Army Intelligence Reserve unit of Dallas, was part of it in his capacity as chief of intelligence for Dallas Civil Defense, which worked out of an underground Emergency Operating Center. As Russ Baker reports, “Because it was intended for ‘continuity of government’ operations during an attack, [the Center] was fully equipped with communications equipment.”54 A speech given at the dedication of the Center in 1961 supplies further details:
This Emergency Operating Center [in Dallas] is part of the National Plan to link Federal, State and local government agencies in a communications network from which rescue operations can be directed in time of local or National emergency. It is a vital part of the National, State, and local Operational Survival Plan.55
Crichton, in other words, was also part of what became known in the 1980s as the Doomsday Project, like James McCord, Oliver North, Donald Rumsfeld, and Dick Cheney after him. But in 1988 its aim was significantly enlarged: no longer to prepare for an atomic attack, but now to plan for the effective suspension of the American constitution in the face of any emergency.56 This change in 1988 allowed COG to be implemented in 2001. By this time the Doomsday Project had developed into what the Washington Post called “a shadow government that evolved based on long-standing ‘continuity of operations plans.’”57
It is clear that the Office of Emergency Preparedness (OEP, known from 1961-1968 as the Office of Emergency Planning) supplies a common denominator for key personnel in virtually all of the structural events discussed here. This is a long way from establishing that the OEP itself (in addition to the individuals discussed here) was involved in generating any of these events. But I believe that the alternative communications network housed first in the OEP (later part of Project 908) played a significant role in at least three of them: the JFK assassination, Iran-Contra, and 9/11.
This is easiest to show in the case of 9/11, where it is conceded that the Continuity of Government (COG) plans of the Doomsday Project were implemented by Cheney on 9/11, apparently before the last of the four hijacked planes had crashed.58 The 9/11 Commission could not locate records of the key decisions taken by Cheney on that day, suggesting that they may have taken place on the “secure phone “ in the tunnel leading to the presidential bunker – with such a high classification that the 9/11 Commission was never supplied the phone records.59 Presumably this was a COG phone.
It is not clear whether the “secure phone” in the White House tunnel belonged to the Secret Service or (as one might expect) was part of the secure network of the White House Communications Agency (WHCA). If the latter, we’d have a striking link between 9/11 and the JFK assassination. The WHCA boasts on its Web site that the agency was “a key player in documenting the assassination of President Kennedy.”60 However it is not clear for whom this documentation was conducted, for the WHCA logs and transcripts were in fact withheld from the Warren Commission.61
The Secret Service had installed a WHCA portable radio in the lead car of the presidential motorcade.62 This in turn was in contact by police radio with the pilot car ahead of it, carrying DPD Deputy Chief Lumpkin of the 488th Army Intelligence Reserve unit.63 Records of the WHCA communications from the motorcade never reached the Warren Commission, the House Committee on Assassinations, or the Assassination Records Review Board.64 Thus we cannot tell if they would explain some of the anomalies on the two channels of the Dallas Police Department. They might for example have thrown light upon the unsourced call on the Dallas Police
tapes for a suspect who had exactly the false height and weight recorded for Oswald in his FBI and CIA files.65
Today in 2011 we are still living under the State of Emergency proclaimed after 9/11 by President Bush. At least some COG provisions are still in effect, and were even augmented by Bush through Presidential Directive 51 of May 2007. Commenting on PD-51, the Washington Post reported at that time,
After the 2001 attacks, Bush assigned about 100 senior civilian managers [including Cheney] to rotate secretly to [COG] locations outside of Washington for weeks or months at a time to ensure the nation’s survival, a shadow government that evolved based on long-standing “continuity of operations plans.”66
Presumably this “shadow government” finalized such long-standing COG projects as warrantless surveillance, in part through the Patriot Act, whose controversial provisions were already being implemented by Cheney and others well before the Bill reached Congress on October 12.67 Other COG projects implemented included the militarization of domestic surveillance under NORTHCOM, and the Department of Homeland Security’s Project Endgame—a ten-year plan to expand detention camps at a cost of $400 million in fiscal year 2007 alone.68
I have, therefore, a recommendation for the Occupy movement, rightfully incensed as it is with the plutonomic excesses of Wall Street over the last three decades. It is to call for an end to the state of emergency, which has been in force since 2001, under which since 2008 a U.S. Army Brigade Combat Team has been stationed permanently in the United States, in part to be ready “to help with civil unrest and crowd control.”69
Democracy-lovers must work to prevent the political crisis now developing in America from being resolved by military intervention.
Let me say in conclusion that for a half century American politics have been constrained and deformed by the unresolved matter of the Kennedy assassination. According to a memo of November 25 1963, from Assistant Attorney General Nicholas Katzenbach, it was important then to persuade the public that “Oswald was the assassin,” and that “he did not have confederates.”70 Obviously this priority became even more important after these questionable propositions were endorsed by the Warren Report, the U.S. establishment, and the mainstream press. It has remained an embarrassing priority ever since for all succeeding administrations, including the present one. There is for example an official in Obama’s State Department (Todd Leventhal), whose official job, until recently, included defense of the lone nut theory against so-called “conspiracy theorists”71
If Oswald was not a lone assassin, then it should not surprise us that there is continuity between those who falsified reports about Oswald in 1963, and those who distorted American politics in subsequent deep events beginning with Watergate. Since the deep event of 1963 the legitimacy of America’s political system has become vested in a lie — a lie which subsequent deep events have helped to protect.72
Peter Dale Scott, a former Canadian diplomat and English Professor at the University of California, Berkeley, is the author of Drugs Oil and War, The Road to 9/11, and The War Conspiracy: JFK, 9/11, and the Deep Politics of War.
His most recent book is American War Machine: Deep Politics, the CIA Global Drug Connection and the Road to Afghanistan.
His website, which contains a wealth of his writings, is here http://www.peterdalescott.net/q.html
Peter Dale Scott is a Research Associate of the Centre for Research on Globalization
Notes
1 Tim Weiner, “The Pentagon’s Secret Stash,” Mother Jones Magazine Mar-Apr 1992, 26.
2 J.A. Myerson “War Is a Force That Pays the 1 Percent: Occupying American Foreign Policy,” Truthout, November 14, 2001, link. Cf. Peter Dale Scott, The Road to 9/11 (Berkeley: University of California Press, 2007), 6, etc.
3 Scott, Road to 9/11, 22, 29, 98.
4 Scott, Road to 9/11, 22, 97.
5 Scott, Road to 9/11, 21, 51-52; Kristol as quoted in Lewis H. Lapham, “Tentacles of Rage: The Republican Propaganda Mill, a Brief History,” Harper’s Magazine, September 2004, 36.
6 E.g. Peter Dale Scott, American War Machine, 204-05.
7 Peter Dale Scott, The War Conspiracy, 354.
8 Peter Dale Scott, Deep Politics II, 30-33; Scott, The War Conspiracy, 387; Scott, American War Machine, 152.
9 Clarence M. Kelley, Kelley: The Story of an FBI Director (Kansas City, MO:
Andrews, McMeel, and Parker, 1987), 268, quoted in Scott, The War Conspiracy (2008), 389.
10 Scott, Deep Politics, 275; Scott, Deep Politics II, 80, 129n; HSCA Critics Conference of 17 September 1977, 181, link. Stringfellow worked under Jack Revill in the Vice Squad of the DPD Special Services Bureau. As such he reported regularly to the FBI on such close Jack Ruby associates as James Herbert Dolan, a “known hoodlum and strong-arm man” on the FBI’s Top Criminal list for Dallas (Robert M. Barrett, FBI Report of February 2, 1963, NARA#124-90038-10026, 12 [Stringfellow]; cf. NARA#124-10212-10012, 4 [hoodlum], NARA#124-10195-10305, 9 [Top Criminal]). Cf. 14 WH 601-02 Ruby and Dolan]. Robert Barrett, who received Stringfellow’s reports to the FBI, had Ruby’s friend Dolan under close surveillance; he also took part in Oswald’s arrest at the Texas Theater, and claimed to have seen DPD Officer Westbrook with Oswald’s wallet at the site of the Tippit killing [Dale K. Myers, With Malice: Lee Harvey Oswald and the Murder of Officer J.D. Tippit (Milford, MI: Oak Cliff Press, 1998), 287-90]).
11 It was sent for information to Washington, which received it three days later (Scott, Deep Politics, 275; Scott, Deep Politics II, 80, 129n; Scott, War Conspiracy, 382).
12 Warren Commission Exhibit 1778, 23 WH 383. (Marina’s actual words, before mistranslation, were quite innocuous: “I cannot describe it [the gun] because a rifle to me like all rifles” (Warren Commission Exhibit 1778, 23 WH 383; discussion in Scott, Deep Politics, 168-72).
13 Stringfellow himself was the source of one other piece of false intelligence on November 22: that Oswald had confessed to the murders of both the president and Officer Tippit (Dallas FBI File DL 89-43-2381C; Paul L. Hoch, “The Final Investigation? The HSCA and Army Intelligence,” The Third Decade, 1, 5 [July 1985], 3),
14 9 WH 106; Scott, Deep Politics, 275-76; Russ Baker, Family of Secrets, 119-22.
15 Rodney P. Carlisle and Dominic J. Monetta, Brandy: Our Man in Acapulco (Denton, TX: University of North Texas Press, 1999), 128.
16 Joint Chiefs of Staff, “Courses of Action Related to Cuba (Case II),” Report of the J-5 to the Joint Chiefs of Staff, 1 May 1963, NARA #202-10002-10018, 12. Cf. pp. 15-16: “The United States should intervene militarily in Cuba and could (a) engineer provocative incidents ostensibly perpetrated by the Castro regime to serve as the cause of invasion…”
17 Robert Dallek, An Unfinished Life, 568; James A. Nathan, The Cuban missile crisis revisited, 283; Waldron and Hartmann, Legacy of Secrecy, 9.
[18 Joint Chiefs of Staff, “Courses of Action Related to Cuba (Case II),” Report of the J-5 to the Joint Chiefs of Staff, 1 May 1963, NARA #202-10002-10018, 12.
19 “Courses of Action Related to Cuba (Case II),” NARA #202-10002-10018, 20. I see nothing in this document indicating that the President should be notified that these “fabricated provocations” were false. On the contrary, the document called for “compartmentation of participants” to insure that the true facts were not leaked (“Courses of Action Related to Cuba (Case II),” NARA #202-10002-10018, 19).
20 Quoted in Baker, Family of Secrets, 122. One of these, DPD Detective John Adamcik, was a member of the party which retrieved a blanket said to have contained Oswald’s rifle; and which the Warren Commission used to link Oswald to the famous Mannlicher Carcano. Adamcik was later present at Mamantov’s interview of Marina about the rifle, and corroborated Mamantov’s account of it to the Warren Commission. There is reason to believe that Mamantov’s translation of Marina’s testimony was inaccurate (Scott, Deep Politics, 268-70, 276).
21 See James Douglass, JFK and the Unspeakable (Maryknoll, NY: Orbis Books, 2008).
22 9/11 Commission Report, 259, 271; Lawrence Wright, The Looming Tower:
Al-Qaeda and the Road to 9/11 (New York: Knopf, 2006), 352–54 (FBI agent).
23 James Bamford, A Pretext for War: 9/11, Iraq, and the Abuse of America’s Intelligence Agencies (New York: Doubleday, 2004, 224. For a fuller account of the CIA’s withholding before 9/11, see Kevin Fenton, Disconnecting the Dots; Rory O’Connor and Ray Nowosielski, “Insiders Voice Doubts about CIA’s 9/11 Story,” Salon, October 14, 2011, link.
24 Fenton, Disconnecting the Dots, 7-12, 142-47, etc.
25 Scott, American War Machine, 203.
26 Fenton, Disconnecting the Dots, 371, cf. 95. Quite independently, Richard Clarke, the former White House Counterterrorism Chief on 9/11, has charged that “There was a high-level decision in the CIA ordering people not to share information” (Rory O’Connor and Ray Nowosielski, “Insiders Voice Doubts about CIA’s 9/11 Story,” Salon, October 14, 2011).
27 Coll, 467-69.
28 Fenton, Disconnecting the Dots, 107-08.
29 James Bamford, Body of Secrets, 201. Cf. Fredrik Logevall, Choosing War: The Lost Chance for Peace and the Escalation of War in Vietnam (Berkeley: University of California Press, 1999), 200, citing John Prados, The Hidden History of the Vietnam War (Chicago: Ivan R. Dee, 1995), 51.
30 “Courses of Action Related to Cuba (Case II),” Report of the J-5 to the Joint Chiefs of Staff, May 1, 1963, JCS 2304/189, NARA #202-10002-10018, link.
31 Peter Dale Scott, Deep Politics and the Death of JFK, 280.
32 Public Law 90-331 (18 U.S.C. 3056); discussion in Peter Dale Scott, Paul L.
Hoch, and Russell Stetler, The Assassinations: Dallas and Beyond (New York: Random
House, 1976), 443–46.
33 Army intelligence agents were seconded to the Secret Service, and at this time there was a great increase in their number. The Washington Star later explained that “the big build-up in [Army] information gathering…did not come until after the shooting of the Rev. Martin Luther King” (Washington Star, December 6, 1970; reprinted in Federal Data Banks Hearings, p. 1728).
34 George O’Toole, The Private Sector (New York: Norton, 1978), 145, quoted in
Scott, Deep Politics and the Death of JFK, 278–79.
35 Scott, Road to 9/11, 52-53.
36 Scott, Road to 9/11, 53-54.
37 Scott, Road to 9/11, 50-64.
38 Peter Dale Scott, “Northwards without North,” Social Justice (Summer 1989). Revised as “North, Iran-Contra, and the Doomsday Project: The Original Congressional Cover Up of Continuity-of-Government Planning,” Asia-Pacific Journal: Japan Focus, February 21, 2011.
39 Scott, Road to 9/11, 132.
40 Jonathan Marshall, Peter Dale Scott, and Jane Hunter, The Iran-Contra Connection, 13 (Contras); Richard Coll, Ghost Wars, 93-102 (mujahedin).
41 Richard Coll, Ghost Wars, 457-59, 534-36,
42 According to testimony from CIA Deputy Director Vernon Walters, only “Hunt and McCord had ever been CIA full-time employees. The others [including Sturgis] were contract employees for a short duration or a longer duration” (Watergate Hearings, 3427). Cf. Marshall, Scott, and Hunter, The Iran-Contra Connection, 45 (casino owners).
43 Peter Dale Scott, “From Dallas to Watergate,” Ramparts, December 1973; reprinted in Peter Dale Scott, Paul L. Hoch, and Russell Stetler, The Assassinations: Dallas and Beyond, 356, 363.
44 Peter Dale Scott, Crime and Cover-Up, 20.
45 Peter Dale Scott and Jonathan Marshall, Cocaine Politics, 25-32, etc.
46 Alexander Cockburn and Jeffrey St. Clair, Whiteout: The CIA, Drugs, and the Press (London: Verso, 1998), 308-09; Martha Honey, Hostile Acts: U.S. Policy in Costa Rica in the 1980s (Gainesville, FL: University Press of Florida, 1994), 368 (Frigorificos).
47 Tad Szulc, Compulsive Spy: The Strange Career of E. Howard Hunt (New York: Viking, 1974), 96-97.
48 Scott, American War Machine, 51-54. Hunt helped put together what became the drug-linked World Anti-Communist League. Artime’s Costa Rica base was on land whose owners were part of the local WACL chapter (Scott and Marshall, Cocaine Politics, 87, 220).
49 Woodward and Bernstein, All the President’s Men (New York: Simon and Schuster, 1974), 23
50 Jim Hougan, Secret Agenda (New York: Random House, 1984), 16, citing Department of Defense Directive 5230.7, June 25, 1965, amended May 21, 1971.
51 Peter Dale Scott, “North, Iran-Contra, and the Doomsday Project: The Original Congressional Cover Up of Continuity-of-Government Planning,” Asia-Pacific Journal: Japan Focus, February 21, 2011. Cf. Peter Dale Scott, “Northwards Without North: Bush, Counterterrorism, and the Continuation of Secret Power.” Social Justice (San Francisco), XVI, 2 (Summer 1989), 1-30; Peter Dale Scott, “The Terrorism Task Force.” Covert Action Information Bulletin, 33 (Winter 1990), 12-15.
52 Peter Dale Scott and Jonathan Marshall, Cocaine Politics: Drugs, Armies, and the CIA in Central America (Berkeley: University of California Press, 1998), 140-41, 242 (Iran, etc.); Ola Tunander, The secret war against Sweden: US and British submarine deception in the 1980s, 309 (Sweden).
53 Scott, Road to 9/11, 183-87.
54 Russ Baker, Family of Secrets, 121.
55 “Statement by Col. John W. Mayo, Chairman of City-County Civil Defense and Disaster Commission at the Dedication of the Emergency Operating Center at Fair Park,” May 24, 1961, link.
Six linear inches of Civil Defense Administrative Files are preserved in the Dallas Municipal Archives; a Finding Guide is viewable online here. I hope an interested researcher may wish to consult them.
56 Scott, Road to 9/11, 183-87.
57 Washington Post, May 10, 2007.
58 9/11 Report, 38, 326, 555n9; Peter Dale Scott, The Road to 9/11: Wealth, Empire, and the Future of America, 224.
59 Scott, Road to 9/11, 226-30. A footnote in the 9/11 Report (555n9) says:
“The 9/11 crisis tested the U.S. government’s plans and capabilities to ensure the continuity of constitutional government and the continuity of government operations. We did not investigate this topic, except as needed to understand the activities and communications of key officials on 9/11. The Chair, Vice Chair, and senior staff were briefed on the general nature and implementation of these continuity plans.”
The other footnotes confirm that no information from COG files was used to document the 9/11 report. At a minimum these files might resolve the mystery of the missing phone call which simultaneously authorized COG, and (in consequence) determined that Bush should continue to stay out of Washington. I suspect that they might tell us a great deal more.
60 “White House Communications Agency,” Signal Corps Regimental History, link.
61 The Warren Commission staff knew of the WHCA presence in Dallas from the Secret Service (17 WH 598, 619, 630, etc.).
62 Statement of Secret Service official Winston Lawson, 17 WH 630 (WHCA radio).
63 Pamela McElwain-Brown, “The Presidential Lincoln Continental SS-100-X,” Dealey Plaza Echo, Volume 3, Issue 2, 23, link (police radio); Scott, Deep Politics and the Death of JFK, 272-75 (Lumpkin).
64 In the 1990s the WHCA supplied statements to the ARRB concerning communications between Dallas and Washington on November 22 (NARA #172-10001-10002 to NARA #172-10000-10008). The Assassination Records Review Board also attempted to obtain from the WHCA the unedited original tapes of conversations from Air Force One on the return trip from Dallas, November 22, 1963. (Edited and condensed versions of these tapes had been available since the 1970s from the Lyndon Baines Johnson Library in Austin, Texas.) The attempt was unsuccessful: “The Review Board’s repeated written and oral inquiries of the White House Communications Agency did not bear fruit. The WHCA could not produce any records that illuminated the provenance of the edited tapes.” See Assassinations Records Review Board: Final Report, chapter 6, Part 1, 116, link. In November 2011 AP reported that Gen. Chester Clifton’s personal copy of the Air Force One recordings was being put up for sale, with an asking price of $500,000 (AP, November 15, 2011, link).
65 See Scott, War Conspiracy (2008), 347-48, 385-87.
66 Washington Post, May 10, 2007.
67 Dick Cheney, In My Time: A Personal and Political Memoir (New York: Threshold Editions, 2011), 348: “One of the first efforts we undertook after 9/11 to strengthen the country’s defenses was securing passage of the Patriot Act, which the president signed into law on [sic] October 2001.” Cf. “The Patriot Act, which the president signed into law on October 2001,″ link; “Questions and Answers about Beginning of Domestic Spying Program; link.
68 Scott, Road to 9/11, 236-45; Peter Dale Scott, “Is the State of Emergency Superseding our Constitution? Continuity of Government Planning, War and American Society,” November 28, 2010, http:/1/japanfocus.org/-Peter_Dale-Scott/3448.
69 “Brigade homeland tours start Oct. 1,” Army Times, September 30, 2008, link. As part of the Army’s emergency plan GARDEN PLOT in the 1960s, there were until 1971 two brigades (4,800 troops) on permanent standby to quell unrest.
70 “Memorandum for Mr. Moyers” of November 25, 1963, FBI 62-109060, Section 18, p. 29, link. Cf. Nicholas Katzenbach, Some of It Was Fun (New York: W.W. Norton, 2008), 131-36.
71 Leventhal’s official title is (or was) “Chief of the Counter-Misinformation Team, U.S. Department of State” (link). In 2010 the U.S. State Department “launched an official bid to shoot down conspiracy theories….The “Conspiracy Theories and Misinformation” page… insists that Lee Harvey Oswald killed John F Kennedy alone, and that the Pentagon was not hit by a cruise missile on 9/11” Daily Record [Scotland], August 2, 2010, (link). The site still exists here, (“Conspiracy theories exist in the realm of myth, where imaginations run wild, fears trump facts, and evidence is ignored.”) The site still attacks 9/11 theories, but a page on the Kennedy assassination has been suspended (link). Cf. Robin Ramsay, “Government vs Conspiracy Theorists: The official war on “sick think,” Fortean Times, April 2010, link; “The State Department vs ‘Sick Think’
The JFK assassination, 9/11, and the Tory MP spiked with LSD,” Fortean Times, July 2010, link; William Kelly, “Todd Leventhal: The Minister of Diz at Dealey Plaza,” CTKA, 2010, link.
72 For Nixon’s sensitivity concerning the Kennedy assassination, and the way this induced him into some of the intrigues known collectively as Watergate, see e.g. Scott, Hoch, and Stetler, The Assassinations, 374-78; Peter Dale Scott, Crime and Cover-up (Santa Barbara, CA: Open Archive Press, 1993), 33, 64-66.
 The Worldwide Corona Crisis, Global Coup d’Etat Against Humanity
The Worldwide Corona Crisis, Global Coup d’Etat Against Humanity